The NSA made SELinux.. can you trust it?
It scores higher on security audits and has more fine-grained control. But should you use it?

MAC
There’s this fancy word called “Mandatory Access Control” or MAC. Don’t be fooled by how big a word it is, it’s simple. It just decides what a file or program can access on the system with clearly defined rules and labels.
Think of the analogy of a nightclub. The bouncer at the front is like the firewall rules or you deciding to download it. But then once it’s inside the club, where can it go? Can it go into VIP? That badge you’d wear for VIP is like MAC, it’s labels that define what stuff can do or access.
SELinux vs AppArmor
There’s two main MACs, SELinux and AppArmor.
SELinux is stronger security, but it’s made by the NSA. AppArmor is less strong, but easier to use.
What has SELinux by default?
All Android phones
Fedora
ParrotOS
What has AppArmor?
Whonix
Tails
Ok so the NSA made SELinux, and it scores higher on security audits and has more fine-grained control. But can you trust it? I’ll present some pros & cons, but keep in mind that this article is heavily biased against authority and not neutral.
Pro: Open Source
It’s open source and been reviewed by many
Con: Bias
Most vocal anti-government groups aren’t well-funded. I question how many independent non-American influenced audits it’s had. You’d need massive expertise and money to do this. Do Russian hackers trust it? Doubt it.
Con: OpenSSL
The NSA backdoored into OpenSSL, which had MANY people review it. [3] This proves both that its possible to deceive rigorous inspection in the real world, and the NSA has a history of doing so.
Con: Underhanded C Contest
It’s also been proven in academic study that malicious code can be inserted even into inspected open source. The contest nicknamed “The Underhanded C Contest” from Binghamton University had contestants purposefully create malicious code to pass open source inspection. Some entries were able to not only pass even strict scrutiny and win, but did so with very low amounts of characters maliciously used. [4] And these are academic students, so if they can do it, then so can the NSA.
Pro: C Contest is kids
I question the skill of the researchers doing the Underhanded C audits compared to SELinux or the Kernel. In fact, it’s in the Linux kernel already. So you can’t hide anyway
Con: Response:
Support for it is not the same as actively using it with it enabled.
That’s like saying owning a gun is the same as shooting your balls off
Pro: Snowden
The only guy I trust, Edward Snowden, promotes GrapheneOS all the time, and that’s SELinux. You’d think he’d mention if he knew the NSA had a backdoor into ALL android phones, and SELinux was made before his leaks.
Con: Schneier
Security expert Bruce Schneier has pointed out the NSA has put backdoors in encryption standards in the past [1], and when he posted about the NSA making SELinux on his own website, he didn’t comment [2]. Which I interpret in my personal subjective analysis that he doesn’t trust it, suspects a backdoor, but can’t prove it.
Pro: Speed
AppArmor starts up slower than SELinux. So Fedora by default is faster than Ubuntu/Debian.
Con: Minor Benefit
True, that’s valid. But keep in mind SELinux is complex, so you’re wasting hours/days learning something to save a second?
Pro: Control
SELinux restricts access by default, which is far more secure than AppArmor’s default permissiveness. Furthermore, SELinux gives much more fine-grained control, by allowing you to label files, which is based on their true purpose. While as AppArmor bases it on the file path, which is a weaker way to do it.
Con: Errors
True. But SELinux is more complex and requires newer users to debug errors. So it’s only more secure if you actually know what you’re doing. Otherwise, you may be allowing malicious software higher access than it needs, just to get rid of confusing errors.
Pro: AppArmor is Basic
That’s a good point, but AppArmor doesn’t even have the ability to do complex setups for large organizations with critical needs.
Con: Complex
If SELinux is so complex, how can we trust these open source audits?
Conclusion
In conclusion, many academic and corporate researchers praise SELinux over AppArmor for security, and it’s easy to see why large organizations use it. However, for a lone wolf individual with an extreme distrust of the NSA, it’s easy to see why they wouldn’t, even if it’s open source. And if you are bugging out bro, consider subscribing on Session messenger with the Session ID: Simple.
The sources for this article can be found here
If you really want to learn and take your privacy to the next level, Learn about HydraVeil, Access our VPN, and subscribe to our new content via: Arweave Video RSS, Podcast RSS, Session list, Nostr, Bastyon, Article RSS, or join the Signal Group
Related Posts
People often confuse privacy and security
Privacy and security are fairly different, here's the key...
[SP]
Jan 17, 2024
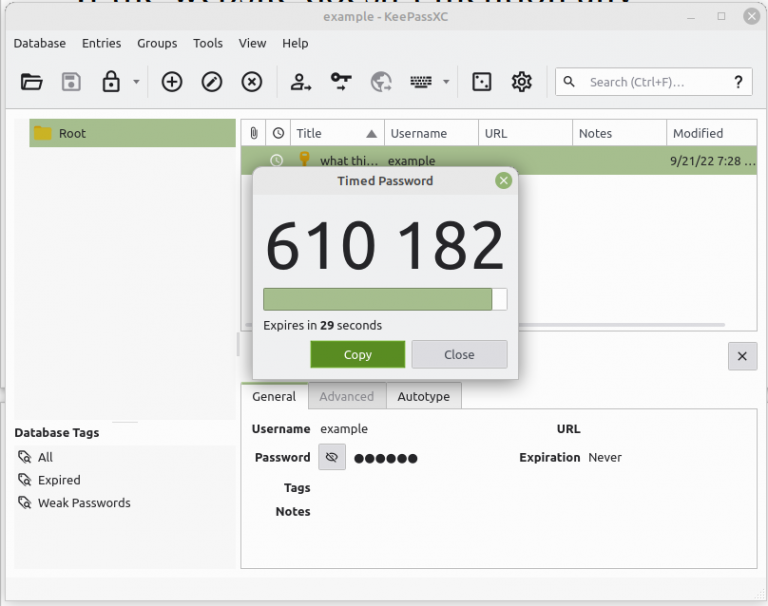
2FA on a PC: KeePass XC Tutorial
Don't use a Phone, do 2FA on your Linux PC
[SP]
Oct 17, 2022
Why to Avoid 2FA on Phones
Avoid SMS and Google, do this instead...
[SP]
Oct 17, 2022