Browser Fingerprinting: What You Need to Know
understand the difference between a cookie and browsing fingerprinting

Update:
Check our new VPN dealing with this issue: https://vpn.simplifiedprivacy.com
Car Metaphor
Tracker on Car
The Electronic Frontier Foundation has a great metaphor to understand the difference between a cookie and browsing fingerprinting. A cookie is like putting a tracker on your car. The tracker’s owner can see everywhere you go until you remove it.
Picture of Car
In contrast, browser fingerprinting is like taking a picture of the car. We know what model, year, license plate number, and state it’s registered.
Fingerprint
With browser fingerprinting, a website records your operating system version, browser type and version, screen dimensions, time zone, IP address, and more. When you take into account all of these different characteristics, it can be a relatively small pool of users whose browsing history shares all these traits.
Not Just IP
Some people mistakenly think that just by changing their IP address with a VPN, it will make them invisible. This is good but not enough, and actually if poorly executed, it could make you stick out to websites even more. If the clock on your local computer is dramatically different than your chosen VPN IP, this makes you stick out as being unique. For example, your local computer’s clock says you’re in the United Kingdom, but your VPN tells a website your IP address is in Japan.
Cross Web
This uniqueness can be tracked across every website you visit and makes it really easy to monitor your traffic. Often different websites will share data with the same large advertising firms (e.g., Google or Facebook) or database tracking brokers such as Oracle.
Tied to Identity
Sign-in
To make matters even worse, you might sign in to a social media account, bank, or some type of service attached to your real identity. Now all of these Big Tech companies and large database brokers know “okay he’s the London Clock with a Tokyo IP, Firefox, 1280 screen dimension, and Windows 11”. How many people share these exact traffic patterns with your identifying characteristics?
Cross-device
Once a computer fingerprint is clearly established as you, the goal of these companies is to fingerprint your phone too, so they can track you across devices. And a phone is much harder to hide a fingerprint on. You aren’t likely to change your screen dimensions on a phone.
How To Defeat Browser Fingerprinting
Update:
Check our new VPN dealing with this issue: https://vpn.simplifiedprivacy.com
There are a few different methods to trick websites and stop big tech companies from browser fingerprinting you. We’ll group these into:
a) Using Browsers with Blocking Features
b) Using Different Browsers
d) Using Virtual Machines
e) Disabling Javascript
f) Using untracked mirror websites that serve content from the tracking sites
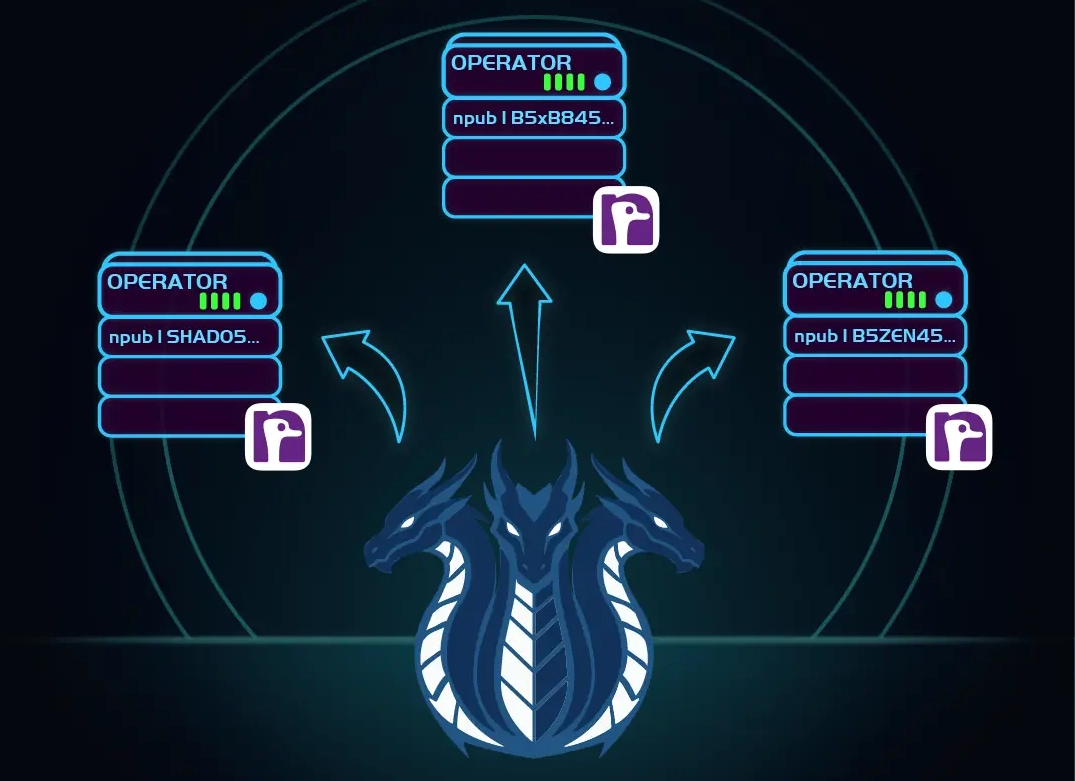
If you really want to learn and take your privacy to the next level, Learn about HydraVeil, Access our VPN, and subscribe to our new content via: Arweave Video RSS, Podcast RSS, Session list, Nostr, Bastyon, Article RSS, or join the Signal Group
Related Posts

Iceland Revamp | HydraVeil Release 2.2.6
Changes to Iceland location
[SP]
Apr 1, 2026

Dynamic Larger Profiles | HydraVeil Release 2.2.5
And two location operators
[SP]
Mar 7, 2026
How HydraVeil Works
Technical Deep Dive: The Yellow Paper
[SP]
Feb 20, 2026
Website Makeover
Learn the Concepts with Awesome Visuals
[SP]
Feb 14, 2026