VPN Mistakes to Avoid
Sometimes people believe that they are getting more privacy or anonymity than they actually are
Mistakes
VPNs are a great tool for privacy, but they are often misunderstood and misused. Sometimes people believe that they are getting more privacy or anonymity than they actually are. Or other times, a user’s goals are possible, but were not executed correctly.
In this article, we will go over some basic common mistakes you should avoid when using a VPN. And to really learn the art of invisibility, subscribe for free to our new content by email, by Session messenger, RSS feed, or Nostr.
Who sees traffic?
First of all, there are many different participants who can view different types of information about what you’re doing online. These include, but are not limited to:
a) Your Internet Service Provider (ISP)
b) The website itself
c) The government
d) Microsoft or Apple (unless you’re on Linux)
e) Google if it’s an Android phone or you’re using Chrome Browser
f) Search engines
g) Cross Site Cookies such as Facebook, Google, Twitter, Amazon, and more which can track you even on a different website.
h) Your router manufacturer, unless you specifically put open source firmware on it
i) Database brokers, such as Oracle, which get contracted to fingerprint your device by some websites and services and then resell that data to advertisers
j) Browser Add-ons may report data back
k) Your DNS or Domain Name Service. Often your ISP will pass this off to Cloudflare or Google
l) Many Websites use Denial of Service (DoS) from Cloudflare and Captchas from Google. These can be sources of tracking.
m) Companies such as Silverpush use ultrasonic audio sounds, which are invisible to the human ear, that are emitted from your computer desktop speakers and picked up on your smart phone, to track you across devices.
So now let’s talk about what a VPN does and does not hide (and what other techniques can be used to help).
VPN Basics
Tunnel
A VPN forms an encrypted tunnel between you and the VPN company. Then whatever you do, is executed from the IP address of the VPN company.
A VPN does hide the following:
a) Your IP address from the website
b) Your traffic from the ISP
c) If properly configured, the VPN should have their own DNS, which will also hide your traffic from the DNS provider that the ISP uses, such as Cloudflare
A VPN does NOT hide the following:
a) The Operating System’s company (e.g., Microsoft, Apple, or Google) phones from knowing the traffic and your true location (IP address)
b) Any type of cross site cookie tracking, such as Facebook
d) Any type of browser fingerprinting from the website or from its third party database broker, such as Oracle. Fingerprinting data include your timezone, your screen dimensions, and operating system version.
e) The government forcing a VPN company to track you in real time
How to Mitigate these issues
Now the cookies issue can be solved by properly modifying your browser settings (and using a good browser).
The Operating system issue can be solved by using Linux or degoogled phones. We covered how Linux works in this article. But if you are insistent on using Microsoft Windows or Apple, then a VPN on the router (instead of the computer itself), could help in some ways, such as hiding your real location.
VPN on a Router
Putting a VPN on a router (instead of the computer itself) hides your IP address (and thus your real location) from Microsoft/Apple. But they can still see the traffic.
Tough in Real World
Now in theory if you never sign in to any account associated with your real name or known nicknames on that device, then it could potentially hide your identity. But in practice, this is highly prone to mistakes in execution, and it’s far better to just use Linux, using Windows or Apple only for specific software you need Windows or Apple for.
Need Firewall
Also putting a VPN on most retail routers will slow down the internet connection, since the processing power on a router is less than real PC CPUs. However, there are more expensive ($200+) firewall routers that can match a computer’s speed because they have real CPU chips inside.
No Logs?
Now let’s talk about logs. Most VPN companies advertise a no logs policy.
This may or may not be true in practice. One can evaluate how the logs policy compares to their other policies.
Crypto
For example does the company accept cryptocurrency? If the traffic data is tied to your real world financial identity, then the company is clearly less committed to keeping you anonymous.
Free VPNs?
Also, free VPNs that don’t cost anything to use should be avoided. They have no profit motive to protect you and usually store and sell data. Why else would they want you to use the service for free?
Tor?
Not only should you only go with VPN providers who accept cryptocurrency, but also make sure they allow sign-ups through Tor. Do they process payments themselves or use a third party like Coinbase which blocks Tor?
Even though you may not use Tor to connect to the VPN, you want to see that they allow customers to actually be anonymous while in compliance with their legal department. This makes it much more likely that their legal structure is set up to resist third party attempts to de-anonymoize users because if the customer used Tor and cryptocurrency, then they can’t identify you.
Legal History
What is the legal history of this VPN company? All of these factors can help you evaluate if you should believe their logging policy.
No Emails
Remember, the VPN company can see your real IP address if you choose to expose it. This IP address can be used to identify you if the internet or real estate is in your name.
While the VPN company seeing your real IP address is necessary if you don’t want to slow the internet connection down with a 2nd VPN or Tor, there is no purpose in the VPN company collecting your email.
Look upon companies that demand an email verification for the VPN with skepticism. Email is usually, under most circumstances, not that secure a protocol. So there is no privacy and anonymity benefit to the end user of the VPN asking for your email.
A reputable VPN company will just give you a bunch of random letters and numbers to login or maybe let you pick a password (but not an email verification). If they only accept a credit card, run away.
No Trust? Use Tor First
If you do not trust a VPN company, but the website blocks the use of Tor, another option is to put a VPN in front of Tor.
You → Tor → VPN → website
This would make it appear as though you’re just using a regular VPN and not Tor to the website. But to the ISP, they would know you’re using Tor but could still not see the contents.
The easiest way to put your traffic through Tor before the VPN is to use a Tor Router.
Also since this VPN would see all the different routes that Tor takes (see our other article on how Tor works), then it’s recommended to use a dedicated VPN that you control/setup on a cloud VPS.
Conclusion
Beyond IP
There are a lot of ways you can be identified beyond your IP address. Some of these include browser fingerprinting, cookies, and the operating system itself spying on you. These things can be avoided by using Linux, virtual machines, and properly configured browser settings.
In general VPNs are an effective tool for many types of traffic, because Tor is slow and often banned. On the other hand, you have to trust the VPN provider to not log or monitor the traffic.
Bird Eye’s View
Look to see the company’s legal history, acceptance of cryptocurrency payments, allowing Tor use, and not requiring pointless data from the user, such as an email.
Big Tech
Corrupt Big Tech does not want you to learn by subscribing to our new content by email, by Session messenger, RSS feed, or Nostr. Here at Simplified Privacy, we can help give custom tailored advice based on your needs. If you are feeling overwhelmed with the technical knowledge of trying to be private, or having issues with a VPN or Tor being banned, reach out to us and chat anonymously.
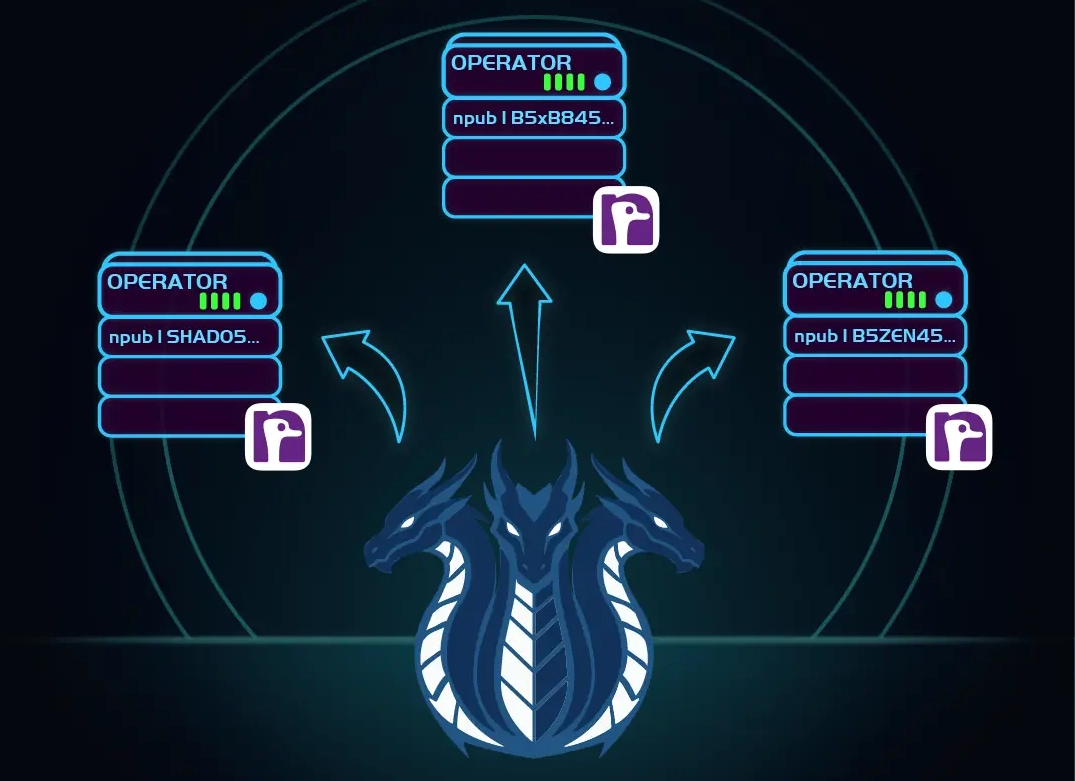
If you really want to learn and take your privacy to the next level, Learn about HydraVeil, Access our VPN, and subscribe to our new content via: Arweave Video RSS, Podcast RSS, Session list, Nostr, Bastyon, Article RSS, or join the Signal Group
Related Posts

Iceland Revamp | HydraVeil Release 2.2.6
Changes to Iceland location
[SP]
Apr 1, 2026

Dynamic Larger Profiles | HydraVeil Release 2.2.5
And two location operators
[SP]
Mar 7, 2026
How HydraVeil Works
Technical Deep Dive: The Yellow Paper
[SP]
Feb 20, 2026
Website Makeover
Learn the Concepts with Awesome Visuals
[SP]
Feb 14, 2026